Digital forensic investigation
Digital forensic investigation
Does my organization need a Digital Forensic Survey?
There are several conceivable scenarios in which digital forensics can help. Has your employee leaked business-sensitive information? Do you suspect theft of intellectual property? Would you like to know whether there is a data breach requiring notification? Do you think your company’s been hacked? Is your integrity at stake? Who’s the sender of the blackmail e-mail? These are all questions that NFIR can answer with its digital forensic investigation. Society is digitized to the point that digital evidence can be found of many acts or actions. For example, almost everyone carries a smartphone in their pocket, which tracks and stores more data than you might think. Computers (both work and personal systems) also often contain treasures of information. The digital forensic investigators at NFIR can conduct investigations on all types of data carriers such as computers, phones, USB sticks and external hard drives, as well as mailboxes, digital documents and files. How successful a digital forensic investigation will be depends on the traces still present, as well as the logging on the systems.
See below for all forms of Digital Forensic Research we perform
Research on computers and laptops
NFIR examines laptops and computers for malware and can help with hacked systems, as well as find out what actions were performed on the system, including recovering deleted data and securing personal documents.
Research on phones
NFIR can secure and extract phones using equipment and software, accessing photos, videos, call history, downloaded files, browser history, GPS data, text messages, chat apps and gyroscope data, among other things.
Fraud investigation
NFIR may investigate digital trails to detect fraud and provide a legitimate interest in conducting a fraud investigation. Fraud can take several forms, including document forgery, scams and credit fraud.
Extortion investigation
NFIR can conduct Digital Forensic Research in extortion cases, but always assesses legitimate interest first. All information is needed for a proper investigation, but NFIR will use discretion and respect the privacy of those involved. With extortion, it is important to report it and preserve communications from the extortionist as evidence.
Investigation into leaks of corporate information
Prevent corporate information leaks by employees with screening, "forensic readiness" and the "need-to-know" principle, but if information is leaked anyway, act quickly and engage NFIR for investigation and legal action.
OSINT research
NFIR conducts Digital Forensic Research, including OSINT (Open Source Intelligence). Among other things, this can help find information about IP addresses, buildings and people. NFIR has knowledge and software to conduct OSINT research more effectively and quickly than an average Internet user.

Investigating transgressive behavior
Digital Forensics can help gather evidence of transgressive behavior, such as sexual assault, harassment and stalking, which can also occur on digital channels.
NFIR Digital Forensic Research
Are you interested in one or more Digital Forensics solutions? If so, please contact one of our account managers.
How does NFIR work?
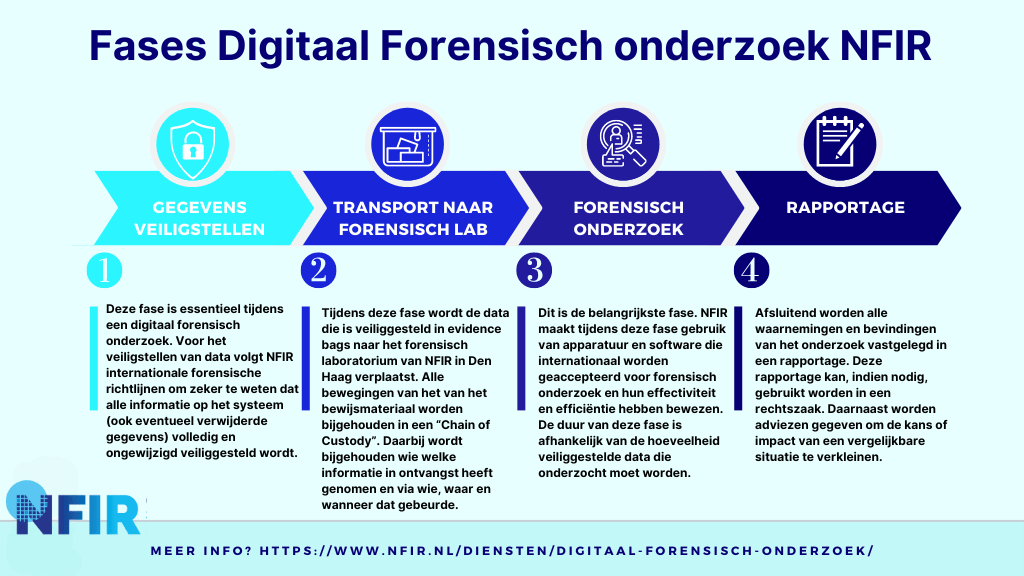
Every digital forensic investigation starts with securing digital traces. This is very meticulous work and a prerequisite for forensic investigation. NFIR therefore only works with internationally approved hardware and software. Technical specialists secure traces on digital data carriers (such as hard discs, flash memory and USB sticks) and make a forensic copy, which will be examined. The study always concludes with a report. All of these phases are clearly depicted in the roadmap below.
NFIR has POB permit 1672 and is supervised by the Department of Justice and Security.
Multidisciplinary forensic research
In digital investigations, traces and data are collected in a forensic way, which makes it possible to reconstruct what happened. The digital traces will be forensically secured and then analysed. The findings of the forensic investigation are incorporated in a clear report.
You can use our report if you want to go to court. If you want to report to another official body (such as the Data Protection Authority), you can also use this report. NFIR cooperates with tactical investigators, privacy lawyers, bailiffs and agencies such as the Police, the NCSC, the Public Prosecution Service and various international services.
Digital forensics?
Use our report in court or when you make a report to another
official body (such as the Data Protection Authority).
An awful lot of different types of information can be found through digital forensics. During the intake, NFIR makes an assessment of the possible tracks and then proposes a plan of action appropriate to the situation. Some examples include example traces in metadata of a file, recovery of deleted files or traces in network traffic.
Metadata can be used to determine, among other things, who the author of a document is or, in the case of a photograph, what type of camera the photograph was taken with. The date a file was created or modified can often be found in this as well.
Recovering deleted data does not always work, but in some cases it is possible. This is possible when the used space on the storage medium has not been overwritten with new data after the original data has been deleted.
Network traffic can also be examined; this may reveal anomalies, such as connections to unknown IP addresses, which are then analyzed further.
Important issues here are the sender’s e-mail address and misspellings in the text. There is often urgency in the email (“Do it now, or your debit card will be blocked!”). You are often asked to click on a link; therefore, always check carefully how the link is constructed (moving the mouse over the link without actually clicking on it often reveals the full link). It is also common to find rogue attachments attached to the e-mail. These files can infect your computer with malware as soon as you download and/or try to open them.
Good “basic hygiene” for your systems consists primarily of using common sense. Be aware of the danger that can lurk in connecting to public networks. It is possible for hackers to get between your device and the connection point, effectively communicating with the hacker instead of the WiFi hotspot. Nowadays, this happens less often because hackers are more likely to look for bigger targets, but the possibility still exists. In addition, always make sure you don’t click on links you don’t trust and don’t just download attachments. Finally, it is important to protect your device with a 6-digit PIN, a password of at least 12 characters or a passphrase.
It is important to disconnect from the Internet immediately. DO NOT turn off your computer/server, this may lose important traces in the computer’s volatile memory. In addition, you can call NFIR at the Emergency Response phone number, which is available 24/7: 088 133 0700.