Get a pen test done now
NFIR holds the CCV quality seal of approval
A pen test demonstrates the technical resilience and effective operation of Security.How secure are your environments?
Get a pen test done now
NFIR holds the CCV quality seal of approval
A pen test demonstrates the technical resilience and effective operation of Security.How secure are your environments?

Certified pentesters
The team consists of certified and experienced Technical Leads and pentesters. Specializing in various environments.
Professional approach
Committed Technical Leads and Project Coordinators ensure high-quality pen testing according to the CCV quality mark.

Extensive experience
Have a pen test performed by a team that performs hundreds of pen tests annually with an average customer satisfaction rating of 8.4

Clear and transparent
The pen test report is clear, complete and actionable. We always provide an explanation and are also available to you after the project.
Pentest of high quality
Certified and quality-oriented pentesters
Pentests are essential to test the technical resilience and effective operation of security. Our pentesters focus on identifying vulnerabilities in systems by deploying various attack techniques. Our skilled and professional pen testers have extensive experience, creativity and up-to-date professional knowledge. The pentesters have completed various relevant training courses and hold the following certifications, among others, OSCP, OSWP, OSWE, OSEP, CPTS, CBBH, and eWPT.
Pentesting and the CCV seal of approval:
- This quality mark, based on NEN-EN-ISO/IEC standards 17021 and 17065, gives customers the guarantee that the execution of a pen testing assignment by NFIR is carried out in a professional and high-quality manner.
- NFIR possesses since 07-01-2022 the CCV quality mark for Pentesting.
I want to pentest my environment(s)!
Once you fill out this form, we will contact you immediately to inform you of the possibilities.
We schedule a no-obligation intake with a Technical Lead to coordinate scope components and attack scenarios.
The findings of the pen test are delivered in a clear, complete and actionable report.
Pentest appointment (ads)
"*" indicates required fields
What environments can we test for you?

Infrastructure pentest
External-, Internal- or Cloud IT infrastructures. Testing laptops, PCs, smartphones or testing the available Wi-Fi on site is also among the possibilities.
Web application pentest
NFIR uses the Web Security Testing Guide (WSTG) for pen testing web applications. This standard gives you the guarantee that the pen test is carried out completely and according to the correct standards.
API pentest
NFIR uses the OWASP Web Security Testing Guide (WSTG) and the OWASP API Security Top 10 for pen testing APIs. This standard gives you the guarantee that the pen test is carried out according to the correct standards and completely.

Mobile application pen test
NFIR uses the OWASP Mobile Application Security Testing Guide (MASTG) for testing mobile applications. This standard gives you the guarantee that the pen test is carried out according to the correct standards and completely.

Operational Technology (OT) pen test
NFIR uses the Penetration Testing Execution Standard (PTES) and best practices, like IEC 62443, for pen testing OT infrastructure.
From pen testing to clear reporting!
Step 1: intake
During the intake, we discuss the scope components and attack scenarios of the pen test. An ethical hacker from NFIR is also present during the intake.
The intake is an important starting point because we would like to test all components within the scope of the pen test and identify all vulnerabilities. Based on the intake, we provide an hourly estimate and proposal.
Step 2: Proposal and agreements
After you receive the hour estimate and proposal, we will be happy to discuss your questions.
In consultation, we will find a suitable time to perform the pen test.
Step 3. implementation
During the pen test, we keep you informed about progress and vulnerabilities.
Critical vulnerabilities are reported immediately so that they can be resolved as soon as possible.
Step 4: Results
The vulnerabilities are documented in a clear and complete pen testing report. A standard part of our pentest services is to explain the findings following the delivered pentest report.
This explanation is greatly appreciated by our clients.
Step 5: Perfecting
Thanks to the clear insights, you are going to mitigate the vulnerabilities.
If required, we can arrange for a retest after the vulnerabilities have been mitigated. Based on this retest, you will receive a new pen test report and have confirmation that the vulnerabilities have actually been fixed
Let us assess your risks!
Find out how safe you really are and contact us today.
Why conduct a pen test at your organization or company?
By performing a pen test at NFIR, you will discover weaknesses in your IT/OT environments. Our ethical hackers identify vulnerabilities and provide insight into the effectiveness of your security measures, as well as potential consequences if misused.
The importance of an enterprise network pen test
The main reasons to perform a proper pen test on the network are:
- Identify vulnerabilities and risks:
Receive an overview report of the vulnerabilities and risks present within your infrastructure and applications. - Building trust:
Customers, shareholders and other stakeholders expect their information to be secure. A pen test provides insight into the level of security. - Comply with standards and legislation:
Various standards and legislation such as the AVG, BIO, ENSIA and ISO, require appropriate security measures to be taken. A pentest helps you meet these requirements. - Continuous security improvement:
The results of the pen test can be used to improve and optimize your information security.
Attack scenarios; Black Box pentest, Grey Box pentest and White Box Pentest.
Perform a pen test from different perspectives, with the result depending (in part) on the chosen attack perspective. During an intake meeting, we jointly determine the scope of the pen test and advise our security specialists/ethical hackers on how to perform the most valuable pen test for your organization.
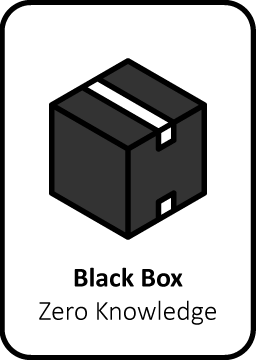
Black Box pentest
In a Black Box Pentest attack scenario, minimal information is provided in advance by the client. Ethical hackers will operate as "outsiders" without inside information. Pentesters use various techniques, including Open Source Intelligence (OSINT) to discover vulnerabilities.
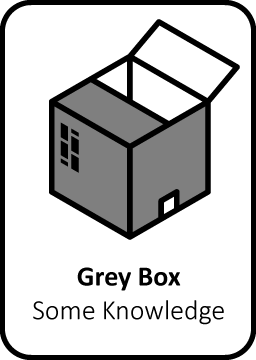
Grey Box Pentest
A Grey Box Pentest attack scenario sits between a Black and White box. There is "limited" sharing of information used to investigate an environment. The ethical hackers will use a user account to examine the infrastructure or application.
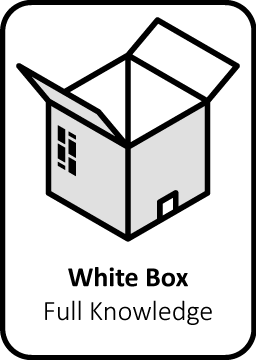
White Box Pentest
In a White Box Pentest attack scenario (also known as Crystal box), all information is provided in advance to search for vulnerabilities in a targeted manner. Consider the information that is also requested in Grey Box pentesting. In addition, source code, log files and server access are used. In addition, the ability to set up your own test environment can be used.
What clients have to say
Pen tests

Ministry of Health, Welfare and Sport
Digital Forensics & Pentesting
Willem van Oranje Onderwijsgroep
Security Monitoring & Pentesting

Royal Hordijk
Frequently asked questions about performing pen testing
What's a pen test?
A pen test, penetration test, or penetration test, is a simulated cyber attack on a system, network, or application to identify and exploit security weaknesses. This helps organizations evaluate and improve their security measures by exposing potential threats and vulnerabilities before malicious actors do.
Corporate network pen test
An enterprise network pen test is an in-depth analysis of your network security. NFIR's experts identify and fix vulnerabilities to protect your corporate network from potential attacks.
How long does a Pentest take?
Depending on the size of the job, a careful assessment is made as to whether multiple people should be put on a pentest to reduce the length of the job. The duration of a pentest can vary depending on the environment being tested and the complexity of the attack scenarios being used. Generally, a pentest covers a period of 2 to 4 weeks. This period includes not only the execution of the test itself, but also the preparation, analysis and explanation of the final report.
When is a Pentest necessary?
A pentest (penetration test) is necessary because companies are often unaware of vulnerabilities in their network and systems. It is a controlled and authorized attempt to evaluate security through a simulated attack. The main reasons for a pentest include vulnerability identification, risk management, regulatory compliance, evaluation of new applications and changes, protection of customer data, and building trust with customers and stakeholders. Conducting regular pentests is essential to improve security and prepare for potential attacks.
- For example, a pen test is useful to:
Assess your current situation for vulnerabilities. - Detect vulnerabilities before the release of new applications.
- Check weaknesses after changes to infrastructure or applications.
- Comply with corporate policies, standards and/or legislation that require periodic security assessments.
- Test your Cybersecurity maturity against the detection methods you have implemented.
What methodologies and standards are used during the execution of a Pentest?
When performing a pentest, various international standards and methodologies are used to discover and classify vulnerabilities.
Some of the key standards applicable to the assignment include:
- Penetration Testing Execution Standard (PTES): methodology for the purpose of infrastructure pen testing.
- OWASP WSTG: Standard for the purpose of Web application pentesting.
- OWASP Top 10: The 10 most critical web application vulnerabilities.
- OWASP API Security Top 10: The 10 most critical API vulnerabilities.
- OWASP MASTG: Standard for the purpose of mobile application pentesting.
- Common Vulnerability Scoring System (CVSS): Used to classify the severity of vulnerabilities.
By using these standards, a pentest can be performed in a structured and thorough manner, and the results can be reported in a clear and comparable way.
Penetration tests by our certified experts
Our pentesters have a large amount of experience, a lot of creativity and up-to-date expertise. The NFIR pentesters have followed relevant training courses and obtained certifications such as OSCP. In addition, they have all received chief of police approval and signed confidentiality agreements.
Black box or white box scenario?
A Black Box pentest means that no information about the environment is shared with the pen testers beforehand. With a pentest based on the White Box principle, all information about the environment is shared in advance. If you are having a pentest performed for the first time and want to get an overall picture of your security, it is useful to have a Black Box pen test performed.

